A domain scan is an essential step in cybersecurity. It comprises meticulously analyzing a domain to reveal potential flaws. These undetectable vulnerabilities can provide opportunities for attackers to compromise your data. By conducting regular domain scans, you can effectively address these threats and strengthen your overall security posture.
- Regular domain scans help detect vulnerabilities before it's too late
- Many scanning tools are offered to aid you in conducting a comprehensive website analysis
- Understanding the results of a domain scan is essential for implementing appropriate security remediation
Data Breach Scan Identifying Exposed Sensitive Data
In today's digital landscape, safeguarding sensitive data is paramount. A comprehensive data breach scan can expose potential vulnerabilities that jeopardize the confidentiality, integrity, and availability of your most valuable data. These scans leverage advanced technologies to identify exposed networks and weaknesses that threat intelligence could exploit to gain unauthorized access. By proactively conducting data breach scans, organizations can reduce the risk of data breaches, protect their reputation, and ensure the trust of their stakeholders.
Scrub Your Online Presence: Internet Removal Tools
In today's digital age, our online presence can trail behind us, often revealing personal information and past actions that we may no longer want exposed. Fortunately, there are a number of proven solutions available to help you remove your digital footprint and regain control over here your online identity.
- Professional Data Erasure Services: These companies specialize in locating and deleting your information from search engines, social media platforms, and other online directories.
- Online Reputation Management Tools: These tools can help you monitor your online presence for negative content and mitigate its impact. Some services even offer positive posting to boost your reputation.
- Self-Service Solutions: You can also take steps to minimize your digital footprint yourself by reviewing your privacy settings, removing unnecessary accounts, and being mindful of the information you post online.
Taking control of your digital footprint is an important step in protecting your privacy and building a positive online persona. By utilizing these available solutions, you can reshape your online narrative and ensure that your digital past does not define your present or future.
Reclaim Your Privacy: DeleteMe and Data Control
In today's virtual world, our personal information is constantly collected and distributed. This presents a significant threat to our privacy. Fortunately, there are solutions available to help us control our records. DeleteMe is one such service that empowers users to reclaim control over their virtual presence.
DeleteMe delivers a range of features designed to assist you in deleting your confidential information from search engine databases. By employing DeleteMe's knowledge, you can limit the amount of data that is viewable to third parties. This could substantially strengthen your security and provide you greater peace of mind.
- Consider the significance of data privacy in today's world.
- Research the capabilities of DeleteMe and other data deletion services.
- Takeaction to protect your personal information online.
Delving into the Web Safely: Domain & Data Security
While the internet offers a plethora/an abundance/a wealth of opportunities for connection and information sharing, it's crucial to prioritize/emphasize/stress your online safety. Domain and data security are fundamental aspects of this endeavor/mission/goal. Understand that not all websites are trustworthy/legitimate/reliable, and malicious actors often employ/utilize/implement deceptive tactics to compromise/violate/jeopardize your information.
- Always/Regularly/Consistently verify/inspect/examine website URLs before submitting/sharing/entering any personal data.
- Utilize/Employ/Leverage strong, unique passwords for each online account and enable/activate/switch on two-factor authentication whenever possible/available/feasible.
- Be cautious/Exercise vigilance/Remain alert of suspicious emails or links, as they can often be deceptive/fraudulent/malicious attempts to steal/acquire/obtain your information.
By practicing/adopting/implementing these simple yet effective measures, you can significantly enhance/improve/strengthen your online security posture and protect/safeguard/preserve your valuable data.
Comprehensive Guide to Online Protection: From Scans to Deletion
Navigating the digital landscape requires a robust understanding of online protection measures. This guide equips you with the strategies to safeguard your information. We'll delve into critical methods like comprehensive scans, virus deletion, and security best practices. By adopting these measures, you can minimize your risk of cyberattacks.
- Continuously update your programs to patch vulnerabilities.
- Implement a reputable security suite program.
- Maintain strong password habits, including diverse passwords for each account.
- Exercise vigilance when clicking on links, especially from suspicious sources.
 Rider Strong Then & Now!
Rider Strong Then & Now!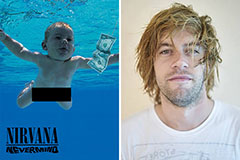 Spencer Elden Then & Now!
Spencer Elden Then & Now! Keshia Knight Pulliam Then & Now!
Keshia Knight Pulliam Then & Now! Stephen Hawking Then & Now!
Stephen Hawking Then & Now! Ryan Phillippe Then & Now!
Ryan Phillippe Then & Now!